Email Authentication in 2026: The Complete B2B Compliance Guide (Gmail, Yahoo & Microsoft)
By the Scrap.io Team · Last updated: March 2026 · 14 min read
18.2% of the top 10 million domains have a valid DMARC record.
That's not a typo. Eighteen percent. The other 82%? Flying blind — and wondering why half their B2B emails end up in spam or get rejected outright.
Meanwhile, domains that actually bother with full email authentication get 2.7× better inbox placement (per Email Vendor Selection's 2025 benchmarks). So we've got this bizarre situation where everyone complains about deliverability... and almost nobody does the one thing that fixes it.
Here's what happened. Between February 2024 and now, Gmail, Yahoo, and Microsoft rolled out email authentication mandates that rewrote the rules for bulk senders. Not guidelines. Not best practices. Mandates. Microsoft will bounce your message with a 550 error if you're not compliant. Gone. Dead. Your prospect never even knows you tried.
I wrote this guide because most articles on the topic are either 500-word summaries that skip the hard parts, or 8,000-word technical manuals written for sysadmins. This one's for the B2B marketer, the founder running cold outreach, the ops person who got tasked with "fixing our email." Practical. Sourced. No fluff.
Video: Email authentication requirements explained — Gmail & Yahoo guidelines
What's inside
- The 2024–2026 enforcement timeline
- SPF, DKIM, DMARC, BIMI, and ARC — what each one actually does
- The real state of email authentication adoption (14 sourced stats)
- The 0.3% spam rate rule + one-click unsubscribe
- What this means for B2B lead gen and cold email
- 5-step setup checklist
- GDPR, CAN-SPAM, TCPA — the compliance layer
- 5 common email authentication mistakes
- Where this is heading in late 2026
- FAQ (11 questions)
The 2024–2026 Email Authentication Timeline: What Changed and Why It Matters
February 2024. Google and Yahoo flip the switch. Any domain pushing more than 5,000 emails per day now must have SPF, DKIM, and DMARC configured. Not "should consider." Must.
That alone was a big deal. But then it snowballed.
May 2025 — Microsoft dropped their own version for Outlook, Hotmail, and Live.com. And they didn't ease into it the way Google did. Gmail started by nudging non-compliant emails into spam. Microsoft? Straight rejection. Error code 550; 5.7.15. Your email doesn't quietly land in a spam folder somewhere. It gets bounced back. Hard bounce. Like it never existed.
September 2025 — La Poste started enforcing authentication on laposte.net. If that name doesn't ring a bell, it's France's national postal service and one of the biggest mailbox providers in Europe. Anybody targeting French B2B contacts? This matters more than you think.
Also in 2025, PCI DSS 4.0 mandated DMARC for every organization processing payment card data. That sounds narrow until you realize it covers SaaS companies, payment processors, e-commerce platforms, and basically anyone with a Stripe integration. Which is... a lot of B2B companies.
And looking ahead — the consensus among deliverability experts points to universal enforcement by late 2026, possibly without volume thresholds at all. Five thousand emails per day won't be the cutoff anymore. Any sender, any volume.
| Provider | Enforcement date | Who's affected | What happens if you ignore it |
|---|---|---|---|
| Gmail | Feb 2024 | 5,000+ emails/day | Spam folder → gradual tightening |
| Yahoo | Feb 2024 | 5,000+ emails/day | Spam folder → gradual tightening |
| Microsoft (Outlook / Hotmail) | May 2025 | 5,000+ emails/day | Immediate rejection (550; 5.7.15) |
| La Poste (France) | Sept 2025 | Bulk senders | Email authentication enforced |
| PCI DSS 4.0 | March 2025 | Payment card processors | DMARC mandatory for compliance |
This isn't a Gmail thing anymore. It's the new baseline.
Email Authentication Protocols Explained: SPF, DKIM, DMARC, and BIMI
Four protocols. Sounds like a lot. It's really not — once you get what each one checks.
SPF (Sender Policy Framework)
One question: "Is this server allowed to send email on behalf of this domain?"
You publish a DNS TXT record listing every IP and service authorized to send as you. Receiving server checks that list. Match = fine. No match = problem. Dead simple in concept.
Example: v=spf1 include:_spf.google.com include:mailgun.org ~all
The trap nobody warns you about: SPF caps out at 10 DNS lookups. Hit 11 and the whole record silently fails. No error. Just... broken. I'll cover this more in the mistakes section because it bites people constantly.
DKIM (DomainKeys Identified Mail)
Think wax seal on a medieval letter. Your server signs every outgoing email with a private key. The receiving server grabs your public key from DNS and checks if the message was altered in transit. If the seal's intact, you're good. If someone tampered with the content mid-route, DKIM catches it.
DMARC (Domain-based Message Authentication, Reporting & Conformance)
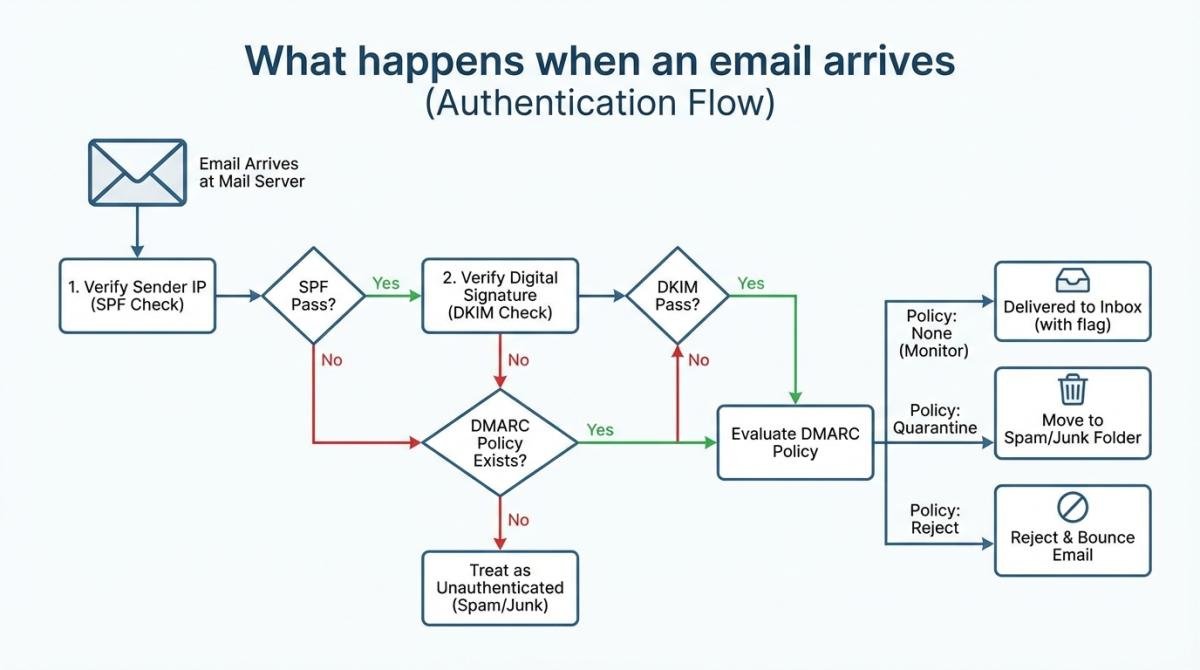
DMARC sits on top of SPF and DKIM. It tells receiving servers: "Here's what to do when something fails."
Three policy levels — and this is where most people get stuck:
p=none — You get reports. Nothing gets enforced. The training wheels option.
p=quarantine — Failed emails land in spam.
p=reject — Failed emails get blocked. Period.
Here's the uncomfortable part. According to Validity's 2025 report, 68% of domains with DMARC are still sitting at p=none. Two years after the mandates kicked in. That's like buying a home security system and leaving the front door wide open.
BIMI (Brand Indicators for Message Identification)
This one's not mandatory. Yet. But it's gaining ground fast — especially in banking, healthcare, and e-commerce.
BIMI lets your brand logo appear next to your emails in the inbox. Gmail supports it. Yahoo supports it. Apple Mail supports it. The requirement? Your DMARC policy has to be at least p=quarantine (so no, p=none won't cut it here either), and you need a Verified Mark Certificate from an authorized CA.
For B2B senders doing high-volume outreach, that logo builds instant trust. When someone sees your icon next to 50 other faceless emails... you stand out. That's worth something.
ARC (Authenticated Received Chain)
Quick one. ARC preserves email authentication results when messages pass through intermediaries — mailing lists, forwarding services, that kind of thing. Without it, a perfectly authenticated email can break DMARC after being forwarded. Google has started referencing ARC in their own documentation. Keep it on your radar.
| Protocol | What it verifies | DNS record type | Example |
|---|---|---|---|
| SPF | Server authorization | TXT | v=spf1 include:_spf.google.com ~all |
| DKIM | Message integrity | TXT (CNAME) | v=DKIM1; k=rsa; p=[public key] |
| DMARC | Policy enforcement | TXT | v=DMARC1; p=reject; rua=mailto:[email protected] |
| BIMI | Brand logo display | TXT | v=BIMI1; l=https://domain.com/logo.svg |
The Real State of Email Authentication: 2026 Statistics That Should Alarm You
OK so the protocols exist. The mandates are live. Gmail, Yahoo, Microsoft — they all enforce now. So surely everyone's caught up?
Not even close.
I pulled numbers from six different industry reports published between Q2 2025 and early 2026. The picture they paint isn't pretty.
Data Innovation — a deliverability consultancy out of Barcelona that works with clients sending 10 billion+ emails per month across 10+ countries — found that senders who upgrade from p=none to p=reject see an 8-12% jump in inbox placement within 60 days. That's massive. Just from changing one DNS record value.
But most people don't. Here are the raw numbers:
Only 18.2% of the top 10 million domains have a valid DMARC record. Just 7.6% enforce it at quarantine or reject. (Both from Fortra, Q2 2025.) Think about that for a second. Ninety-two percent of major domains aren't enforcing email authentication at all.
EasyDMARC's 2025 adoption report shows DMARC adoption grew from 27.2% to 47.7% between 2023 and 2025. Good trajectory. Still means over half of all domains haven't even started.
Authenticated senders reach inboxes 2.7× more often than unauthenticated ones (The Digital Bloom, 2025). Average inbox placement sits at 83.1% (Landbase, 2026). But Office365 inbox placement dropped 26.7 percentage points year-over-year — which tells you Microsoft really isn't kidding around with enforcement.
The security angle matters too. IBM's 2025 Cost of a Data Breach report pegs the average phishing breach at $4.88 million. PowerDMARC estimates 3.4 billion phishing emails go out daily. And per Validity's deep dive on DMARC adoption, 84% of email-sending domains lack a published DMARC record entirely.
Oh, and 57.3% of B2B senders authenticate (Email Vendor Selection, 2025). Which means 43% of people doing B2B email — cold outreach, newsletters, sales sequences — are sending from unauthenticated domains. In 2026. Wild.
One stat that actually gives me hope: when the US government mandated DMARC for federal agencies, successful phishing delivery dropped from 69% to 14% (EasyDMARC, 2025). Proof the system works. When people actually use it.
The 0.3% Spam Rate Rule and One-Click Unsubscribe
Email authentication is one half. The other half is behavioral — and this is where a lot of B2B senders trip up without realizing it.
The rule: keep your spam complaint rate under 0.3%. Three complaints per thousand recipients. Google actually recommends staying below 0.1%, which is tighter than most people assume.
Blow past 0.3% and your emails start landing in spam — or get blocked entirely. And here's the thing most people miss:
That 5,000-email threshold? It counts everything. Marketing emails, transactional emails, password resets, invoice notifications, calendar invites — all of it, from every app sending as your domain. I've seen companies trip the bulk sender requirements because their helpdesk tool was blasting confirmation emails they'd forgotten about.
Microsoft's enforcement is harsher than Gmail's or Yahoo's. Gmail gave senders a grace period. Microsoft didn't. If your Outlook deliverability tanked sometime after May 2025, start by checking your email authentication setup. Seriously. Before you troubleshoot anything else.
On unsubscribe: one click means one click. Not "click here then confirm on this page then answer a survey." One action, done. And you've got 48 hours to process it. That deadline is non-negotiable.
Track your spam rate with Google Postmaster Tools — free, and it shows you exactly how Gmail perceives your domain. If you want a deeper dive on staying out of spam folders, we put together a full guide on avoiding spam in prospecting.
Impact on B2B Lead Generation and Cold Email Outreach
Alright, here's where it gets personal.
If you're sending cold email — and I know a lot of you reading this are — these email authentication rules apply to you. Fully. The fact that your prospect didn't opt in changes nothing about SPF, DKIM, or DMARC requirements. Every cold email you send counts toward your volume, your spam rate, your sender reputation. All of it.
A 6-person marketing agency in Austin isn't hitting 5,000 emails a day. Fair. But Gmail and Yahoo explicitly recommend ALL senders implement authentication regardless of volume. And as enforcement tightens through 2026 (Microsoft already proved they don't play around), the recommendation becomes a requirement overnight. You don't want to be scrambling when that happens.
There's a direct, measurable link between contact data quality and email deliverability. Send to old addresses → bounces pile up → sender reputation craters → even your good emails to real prospects end up in spam. Classic death spiral. (We've got a detailed walkthrough on email validation for 95%+ deliverability and another one on hard bounces vs soft bounces if you're dealing with that right now.)
And if you're not sure where the legal lines are — whether cold emailing is even legal in your market — start there. Authentication is mandatory, but it's not the whole story. You also need the right cold email tools that handle warm-up, rotation, and deliverability tracking out of the box.
Platforms like Scrap.io let you pull verified B2B contact data straight from Google Maps — with a free trial and 100 leads to test. Real-time extraction means fresh data, fewer bounces, and a sender reputation that doesn't implode after your first campaign.
5-Step Email Authentication Setup Checklist
Don't know where to start? This sequence works. (For the full technical walkthrough with copy-paste DNS record examples, see our complete SPF, DKIM and DMARC setup guide — it covers what this article intentionally skips to avoid cannibalizing the how-to angle.)
- Audit every service sending email as your domain. Your ESP, your CRM, your helpdesk, your billing tool, your project management app — anything pushing email from @yourdomain.com. I've audited setups where the company had forgotten three different SaaS tools were sending automated emails on their behalf. You can't protect what you don't know about.
- Create your SPF record. List every authorized sender. Stay under 10 DNS lookups. (Use a tool like MXToolbox to verify before publishing — I cannot stress this enough.) Remove old services you've cancelled but never cleaned out of your DNS.
- Configure DKIM signing. Do it through your email provider's admin panel — Google Workspace, Microsoft 365, Mailgun, SendGrid, whatever you use. Critical detail: sign with YOUR domain, not the provider's default domain. DMARC alignment breaks otherwise.
- Publish a DMARC record. Start at
p=none. Collect reports for 2-4 weeks. See who's sending as your domain (legit and otherwise). Move top=quarantine. Thenp=reject. Don't rush straight to reject unless your audit was truly exhaustive. - Monitor. Continuously. This isn't a set-it-and-forget-it situation. Use Google Postmaster Tools for spam rate visibility. Parse your DMARC aggregate reports with a free tool like DMARCian or Postmark's monitor. New services get added to your stack all the time — each one is a potential gap.
Official references: Google's email authentication guide and Microsoft's authentication documentation.
Once your email authentication is solid, the next move is scaling without wrecking deliverability. We covered that in our guide to automating email outreach with Google Maps data.
Want to put your freshly authenticated domain to work? Start with 100 free verified leads on Scrap.io — B2B contacts extracted from Google Maps in real-time. No stale CSVs from 2023.
Compliance Beyond Authentication: GDPR, CAN-SPAM, and TCPA
Email authentication proves you're you. Compliance proves you should be emailing someone in the first place. Different problems. Both mandatory.
CAN-SPAM (US) — Every commercial email needs a valid physical address, honest subject line, clear sender identification, and a functioning unsubscribe link. Fines go up to $51,744 per violation. (Yes, per email.) One thing CAN-SPAM doesn't require? Prior consent for B2B outreach. That's a crucial distinction from European rules. But "no consent required" doesn't mean "no rules apply." Far from it.
GDPR (EU) — Emailing EU contacts? You need a lawful basis. For B2B cold email, "legitimate interest" is what most companies lean on — and it works, provided you offer easy opt-out, collect minimal data, and can explain how you got their address. If you're weighing the double opt-in vs single opt-in debate, that article walks through the tradeoffs with real case studies.
TCPA (US) — Mostly governs phone and SMS, but if your campaigns combine email with phone outreach (common in B2B), the fines hit hard: $500 to $1,500 per unsolicited contact.
Authentication gets your email delivered. Compliance keeps you out of court. You need both.
Common Email Authentication Mistakes (And How to Fix Them)
Five mistakes. I see all of them constantly. Every single one is fixable.
1. SPF record exceeding 10 DNS lookups. Hard cap. Non-negotiable. Hit 11 and the record fails silently — no error message, no log entry, nothing. Your emails just start failing SPF checks and you have zero idea why. Use an SPF flattener, or (better) go through your includes and remove any service you cancelled six months ago but never cleaned out of DNS.
2. DKIM signing with the ESP's domain. Tons of email providers default to signing outbound email with their own domain, not yours. Technically, the DKIM check passes. But DMARC alignment fails because the DKIM signing domain doesn't match your From address. Always — always — configure DKIM to sign with your own domain. This trips up more people than any other single issue.
3. Parking at p=none indefinitely. 68% of domains with DMARC do exactly this (Validity, 2025). A p=none policy collects reports but enforces nothing. Zero protection. It's the email equivalent of installing security cameras and never plugging them in. Map out a 30-60-90 timeline: none for monitoring, quarantine for testing, reject for production.
4. Ignoring DMARC reports. You set up DMARC. Reports start flowing in. XML files land in that rua mailbox you configured. And... nobody looks at them. Ever. Those reports show every service sending email as your domain — authorized and unauthorized. Free tools like DMARCian parse them into readable dashboards. Takes five minutes to set up. Could save your domain reputation.
5. Forgetting about subdomains. Main domain locked down at p=reject? Great. But what about marketing.yourdomain.com? Or support.yourdomain.com? By default, subdomains inherit the organizational domain's DMARC policy. But if your subdomain policy isn't explicitly defined, attackers can spoof those subdomains instead. Close the gap.
Looking Ahead: Email Authentication Trends in 2026 and Beyond
What we have now isn't the finish line. A few things to watch.
DMARCbis (a.k.a. DMARC2) — Next-gen standard in active development by the IETF. New tags like t=y for testing, psd=y for public suffix domain policies, np= for non-existent subdomains. Nothing's finalized, but the working group is moving. Don't panic about this one. Do keep an eye on it.
BIMI is going mainstream. What started as an experiment is now live at major banks, insurance companies, and health systems. If your competitor's logo shows up in Gmail next to your faceless email — that's a trust gap you're handing them for free.
The AI phishing angle is real. Large language models can now generate impersonation emails that are genuinely hard to spot by eye. The technical signals from email authentication — SPF pass, DKIM valid, DMARC aligned — are becoming the primary defense against AI-crafted phishing. Not the human reader. The protocol stack.
MTA-STS (Mail Transfer Agent Strict Transport Security) is getting traction too. It enforces encrypted TLS connections for email in transit, blocking downgrade attacks. Think HTTPS enforcement, but for SMTP routing.
My prediction — probably shared by most people in the deliverability space — is that volume thresholds disappear by end of 2026. Universal email authentication enforcement, regardless of whether you send 50 emails or 50,000. The writing's been on the wall since February 2024.
FAQ: Email Authentication Requirements in 2026
How do I authenticate my email?
Three DNS records: SPF to authorize your sending servers, DKIM to add a cryptographic signature, DMARC to set your enforcement policy. Most email providers (Google Workspace, Microsoft 365, etc.) have built-in setup wizards. Our complete SPF, DKIM and DMARC setup guide walks you through every step with examples.
How do I check if my email is authenticated?
Fastest way: send a test message to a Gmail account, open it, click "Show original." You'll see SPF, DKIM, and DMARC pass/fail results right there. For DNS-level checks, use MXToolbox, Mail Tester, or Google's Check MX tool. Takes 30 seconds.
What are the new email authentication requirements for Gmail and Yahoo?
Bulk senders (5,000+ emails/day) must have SPF, DKIM, and DMARC. They must include one-click unsubscribe. Spam complaint rate must stay under 0.3%. These gmail email authentication requirements took effect February 2024 and enforcement has been escalating steadily.
When did Microsoft join?
May 5, 2025. Microsoft's email authentication outlook requirements now match Gmail and Yahoo's scope but with harder enforcement — immediate rejection instead of spam filtering. Error code 550; 5.7.15. No second chances.
What happens if you don't comply with email authentication requirements?
Gmail and Yahoo route your messages to spam first, then escalate. Microsoft rejects outright. Beyond inbox placement: domains without authentication are trivially easy to spoof. You're essentially handing attackers a blank check to impersonate your brand.
What is the 0.3% spam rate requirement?
Max 3 spam complaints per 1,000 recipients. Google's recommendation is actually tighter — under 0.1%. Exceed the threshold and you'll see blocking, spam folder placement, or both. Monitor it through Google Postmaster Tools. Fresh, verified contact lists — like those from Scrap.io — help keep complaint rates low because you're reaching real people at real businesses, not dead addresses.
What is BIMI email authentication and do I need it?
BIMI shows your brand logo in the inbox (Gmail, Yahoo, Apple Mail). Requires DMARC at p=quarantine or p=reject, plus a Verified Mark Certificate. Not required by any provider... yet. But it's a trust signal worth pursuing if you're doing serious B2B outreach volume.
Do email authentication requirements apply to small businesses?
The 5,000/day threshold targets bulk senders specifically. But Google and Yahoo recommend ALL senders set up email authentication. Smaller businesses benefit from better deliverability plus protection against domain spoofing. And when thresholds inevitably drop, you'll already be compliant.
What's the difference between Gmail, Yahoo, and Microsoft email authentication requirements?
All three demand SPF, DKIM, DMARC, one-click unsubscribe, and sub-0.3% spam rates. The difference is teeth. Gmail and Yahoo started with spam folder filtering, then escalated. Microsoft went to rejection from day one. Build for the Microsoft standard and you're covered everywhere.
How do I set up SPF, DKIM, and DMARC?
SPF: TXT record listing authorized servers. DKIM: key pair generated through your email provider, public key published in DNS. DMARC: TXT recordwith your policy. Start at p=none, watch reports for 2-4 weeks, escalate to quarantine, then reject. Full DNS examples in our technical setup guide.
Does email authentication apply to cold email?
100%. Cold email is still email. Every authentication requirement applies regardless of opt-in status.And honestly? Because cold email generates more spam complaints than opt-in campaigns, email authentication matters even MORE for cold senders. Get your protocols right first — then focus on writing cold emails that actually get responses.
Try Scrap.io free — get 100 verified B2B leads instantly and put your email authentication to work. Fresh contacts pulled from Google Maps in real-time. No stale databases. No bounced emails wrecking your sender reputation.
More email outreach strategies, templates, and tools: email outreach resource hub.
Ready to generate leads from Google Maps?
Try Scrap.io for free for 7 days.

